Challenges of document design from the viewpoint of available space
Battle for space…sounds like a title of an episode from Star Trek. But, when the design of a new ID document begins, immediately starts a “fight” for space. It is so, even if the players do not realise it. They want to ensure that the features they are responsible for, will appear on the document.
But the space on a document is limited.
In this article we are going to analyse some key aspects of these issues based on the experiences of our experts.
- Expression of the national character – demands of the customer
Once the creation of a new document is decided the customer (usually directly linked to politics) in most cases insists to express some kind of national character. Our professionals have vast experience designing a document that is contemporary in every aspect but they need help to start. Browsing the internet for some characteristic motifs and colours are not enough. They need deeper understanding! Choosing a symbol that we might think is typical, may be inappropriate to some people whose traditions we are not familiar with.
The usage of the colours of the national flag is a quite common requirement. The basic problem is simple: flags always show strong colours (blue, red, black etc.) while the background of an ID should be subtle because it should not interfere with the data, photo, logos, coat of arms etc. that is hardly possible on a dominant background.
The Icelandic driving licence designed and produced by ANY PLC shows a good example of balanced visualisation of national colours.
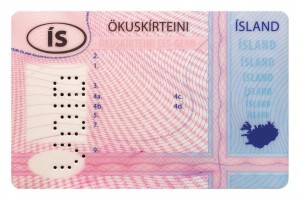

Icelandic driving licence and the national colours
2. Data to be recorded – demands of the issuing entities
Data to be recorded in the card is the responsibility of the issuer (that is often an authority). They often require simply too much data to be presented in the document. On one hand it’s a legitimate need but on the other hand it would result confusion. The alphanumerical information and the photo may become so small that may challenge the security of the document!
What can be the key of this situation?
During regular consultations our designers and security experts collaborating with the issuer’s representatives can create a well-balanced document.
In the rush for a new document the relatively slow process of consultations may seem to be a waste of time, but it is inevitable in order to create a contemporary document.
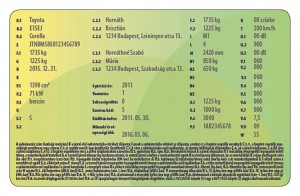
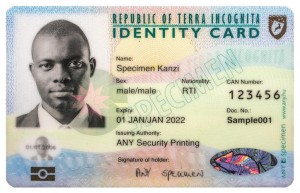
An overcrowded document A well-balanced example
3. Decentralised document issuance – demands of the technology
Our specialists have vast experience with running systems of decentralised personalisation based on security ink-jet printers for almost two decades. They declared, if a few basic rules are obeyed the systems run safely in office environment, operated by the staff, using reasonably priced standard office printers equipped with security inks.
The main conditions that should be considered during the process of the design:
– the selected paper should be secured and should be suitable for water based inks
– the background design should be subtle
– the security features of the ink-jet printed data and the offset printed elements should not interfere
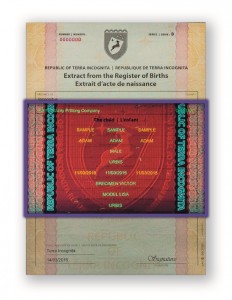
A sample breeder document under UV
4. Demands of the security
Apart from the security elements recommended by the ICAO standard our security specialist suggests to use a few unique ones:
– special bi- and trifluorescent inks
– invisible IR fluorescent inks with or without up-converting features
– fluorescent inks having complex IR spectrum
– combination of colours having the same visible colour but different in IR absorbance or fluorescent features
– special graphic design elements like: Dual-line Multi-level Relief, Line-width and Shape Modulated Linework,
positive-negative Guilloche, modulated Microtext, Custom Screen Pattern.
Custom Screen Pattern (Microtext screen) Dual-line Multi-level Relief
Our specialist said, that the security level of those systems (like VerifIR system e.g.) that require a dedicated device to control a specific security feature is much higher that can be revealed by simple devices. These systems are able to retain the simplicity of control of a second level security device while offers the security of a third level feature.

A handheld verification device
